The Macro: Developers Are One Bad Extension Away From a Very Bad Day
Here’s the thing about developer tooling security: nobody thinks about it until something explodes. The npm registry has had multiple high-profile malicious package incidents. VS Code extensions have shipped with hidden cryptominers. AI models on Hugging Face can carry poisoned weights. And yet the average developer’s vibe check before installing something is roughly: does it have stars on GitHub and does the README look like a human wrote it.
That is not a security posture. That is vibes.
The threat surface has genuinely expanded. More developers are pulling from more registries, running more AI models locally, and installing more IDE extensions than ever before. The MCP server space alone is exploding right now, and according to a LinkedIn post from the Koidex team, they reportedly discovered the first real-world example of a spoofed MCP server, something called PostMark-MCP that looked completely legitimate on first inspection. That kind of attack is subtle, hard to catch manually, and exactly the kind of thing that slips through when your security workflow is just “it looked fine to me.”
Which, look, there are tools in this space. Snyk has been doing dependency scanning for years. Socket.dev watches npm packages for suspicious behavior. GitHub’s Dependabot pings you about known CVEs. These are real products with real traction, especially in enterprise environments where someone has already had a scary conversation with legal.
But most of them are either deeply integrated into CI/CD pipelines, aimed at security teams rather than individual developers, or focused narrowly on one registry. None of them felt like something a solo developer or small team would actually open on a Tuesday afternoon before installing a random JetBrains plugin. That gap is exactly where Koidex is trying to sit.
The Micro: A Safety Search Bar That Actually Understands the Problem
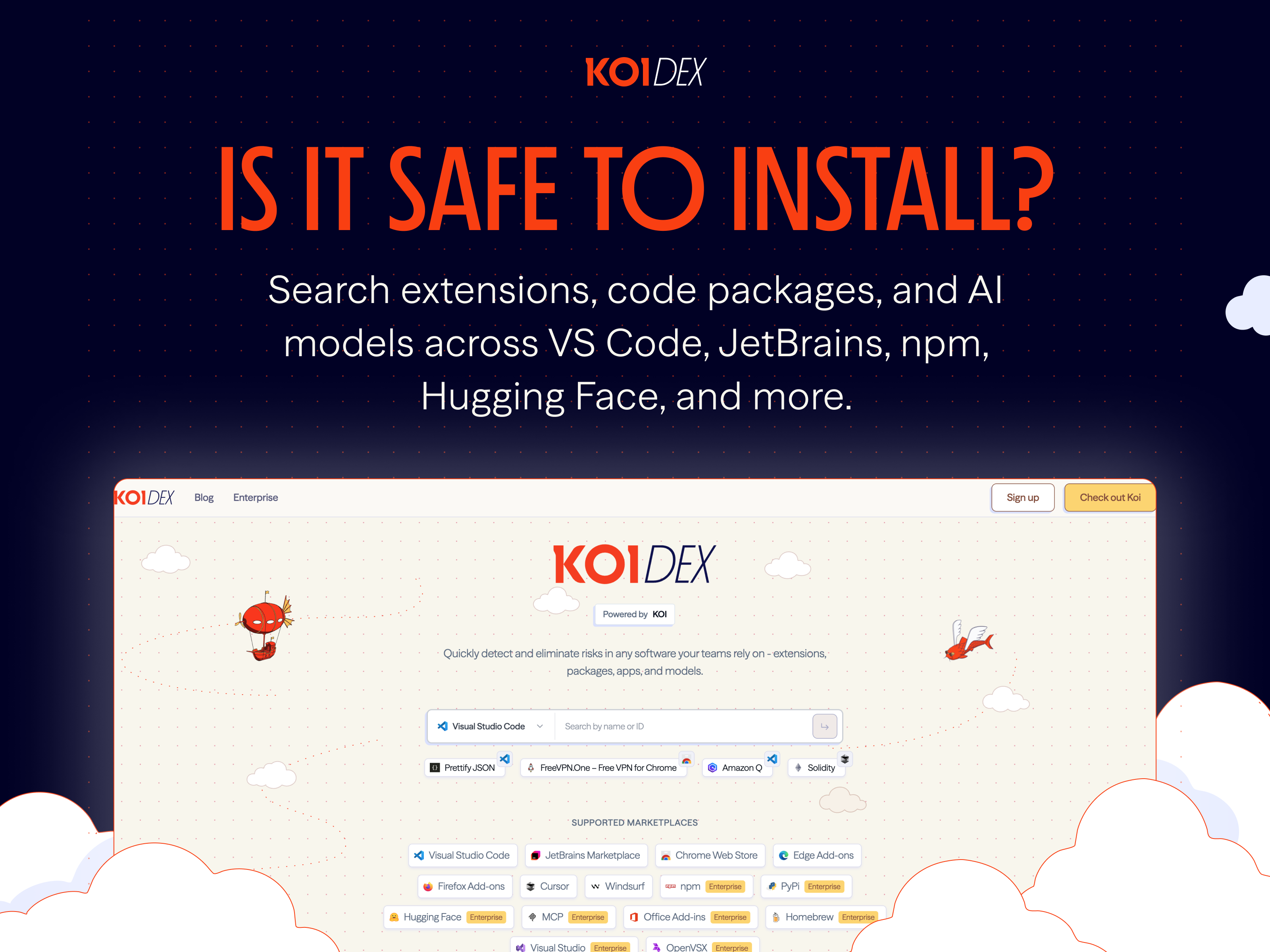
Koidex is simple to describe. You search for a package, extension, or AI model and it tells you whether it looks safe to install. That’s it. Free, no setup required, no account wall in front of the thing you actually need.
The product covers VS Code extensions, JetBrains plugins, npm packages, and Hugging Face models. Four registries, one search box. For developers who bounce between those environments regularly, which is most of them at this point, that cross-registry coverage is genuinely useful. I’d normally have to go check four different places, read changelogs, Google the publisher name, and still feel vaguely uncertain.
There’s also an IDE extension that does real-time background scanning inside Cursor and Windsurf specifically. That targeting is an interesting call. Cursor and Windsurf are both AI-first coding environments that have had explosive growth with the vibe-coding crowd, people who move fast and install things constantly. Scanning in the background while those users work is a smart place to intercept risky behavior without asking anyone to change their habits.
The QuantumWarp notes I found reference an earlier version of the product, suggesting this has been in some form of development for a while, with the current Koidex being a refined iteration. That kind of iteration before a public push usually means the core detection logic has had time to mature, which matters a lot in security tooling where false positives destroy trust fast.
It did well when it launched, hitting the top spot on launch day, with solid engagement in the comments.
The team appears to be based in Israel, with at least one member, according to LinkedIn, having a background at Google. The security research they’re doing seems active, not just a wrapper around existing CVE databases. That PostMark-MCP discovery suggests they’re finding things proactively, which is the difference between a lookup tool and something that’s actually ahead of threats.
For developers already using tools like PinMe’s zero-friction deployment approach or experimenting with AI-assisted coding setups, adding a lightweight safety check to that workflow costs almost nothing.
The Verdict
I think this is a real product solving a real problem. I also think the path to it mattering long-term is harder than the launch makes it look.
The free, no-setup positioning is correct. This needs to be the thing you open without thinking, not another tool that requires an API key and a Slack integration before it shows you anything useful. That instinct is right.
But here’s the thing: discovery and habit formation are brutal in developer tooling. Snyk won because it got into CI/CD and stayed there. If Koidex lives only as a search tab you remember to visit, retention is going to be rough. The IDE extension is probably the more important product, and I’d want to know how far they plan to push it beyond Cursor and Windsurf. VS Code native support would change the calculus significantly.
The MCP security research angle is the most interesting thing about them right now. If they keep publishing findings like the PostMark-MCP discovery and position themselves as the team that actually watches this space, that builds credibility in a way that no amount of product polish can shortcut.
At 90 days, the question I’d be asking is: are developers installing the extension and keeping it, or searching once and forgetting the URL. That number tells you everything.
Also featured on HUGE: Maige Thinks Your Issue Tracker Is Broken and AI Should Run It · PinMe Wants You to Deploy a Website Before You Even Remember to Make an Account · Superset Wants to Be the Air Traffic Controller for Your AI Coding Agents
